Thomas Matthew Crooks — An Attempted Assassination, Botched Candidate Protection, and Conspiracy Theories That Do Not Match Reality
Introduction
On July 13, 2024, a 20-year-old named Thomas Matthew Crooks climbed onto the roof of an industrial building just beyond the fence line of the Butler Farm Show grounds in western Pennsylvania and opened fire on a campaign rally for former President Donald J. Trump. One round grazed Trump’s right ear. Another killed Corey Comperatore, a 50-year-old former fire chief attending with his family. Two more spectators were wounded. Seconds later, return fire from a counter-sniper killed Crooks on the roof. The event lasted seconds; its consequences continue to unspool.
The attempted assassination ignited three overlapping crises. First, an operational failure: obvious high ground outside the hardened perimeter had not been brought under positive control, and a critical counter-drone layer was not effectively operating. Second, a political shock: a moment that became electoral iconography within hours. Third, an information war: a blizzard of conspiracies that mistook ambiguity for proof.
This article reconstructs Crooks’s background and trajectory, the operational failures that made his breach possible, and the information battles that followed. It does not supply motives where none are documented, nor does it indulge in armchair psychology. Where the public record is silent, it stays silent. Where there is ambiguity, it labels it as such. And where misinformation has spread, it confronts it with verifiable facts drawn from official reviews and high-confidence reporting as of August 19, 2025.
Suburban Origins, Ordinary Surfaces
Crooks grew up in Bethel Park, a suburban municipality south of Pittsburgh defined by cul-de-sacs, pickup trucks, two-car driveways, and commercial corridors of chain stores and service businesses. It is the kind of place designed to keep big problems at the edge of town. Neighbors and classmates later described him as quiet, intelligent, and hard to read—present but peripheral. Teachers recalled competence in math and technical coursework and less enthusiasm for group projects or public presentation. He graduated from Bethel Park High School in 2022, without disciplinary history and without the kind of footprint that usually draws institutional attention.
Family portraits that made their way into the record present a stable middle-class household: steady work, routines, and no public evidence of abuse, poverty, or chronic crisis. Socially, he did not register as a joiner. He did not cultivate a conspicuous online persona; when friends and classmates searched for his digital footprint after Butler, they often found very little. Those threads—quiet competence, privacy, and limited social integration—recur across interviews conducted after the fact.
After high school, Crooks attended the Community College of Allegheny County (CCAC) to study engineering science. He finished an associate degree in May 2024 and prepared to continue his studies, with reporting indicating an acceptance to the University of Pittsburgh and a plan to enroll at Robert Morris University for mechanical engineering in the fall. He worked part-time as a dietary aide at a skilled-nursing facility. Supervisors and coworkers later described him as punctual and private.
There is no credible record of sustained extremist organizing in his background, no criminal history that foreshadowed a violent breach, and no confirmed pattern of reported bullying beyond anecdote. Friends and classmates remembered social awkwardness, not menace. If there is an archetype here, it is the ordinary young man who passes undisturbed through familiar institutions, noticed less for what he says than for what he withholds.
Range Logs, Components, and the Compartmentalized Turn
By mid-2023 the surface ordinariness had a countercurrent: a methodical, compartmentalized preparation. Crooks obtained an AR-15–style rifle via a private sale from his father for $500, joined Clairton Sportsmen’s Club about nine miles from home, and began signing the range log again and again. Records reviewed by journalists document more than forty visits over eleven months leading up to the rally—evidence of consistent practice. He was at the range on July 12, the day before the attack.
Investigators later recovered two fully assembled improvised explosive devices (IEDs) configured for remote detonation from Crooks’s vehicle, plus a partially assembled device at his home. Purchase records and emails show orders of nitromethane and the transmitter-receiver electronics needed for remote actuation. Technical assessments concluded the assembled devices could have caused injury or death if triggered properly. He did not use them at Butler.
In parallel, he made a privacy pivot: an encrypted email account, VPN usage, and a browsing pattern that increasingly focused on ballistics, protective doctrine, public-figure movements, and historical assassinations. Investigators and independent reporters documented searches referencing counter-sniper teams, how far a bullet travels, rally schedules, and the geometry of prior shootings. That digital trail is operational, not rhetorical. It reads like preparation, not proclamation.
This is behavior first, not ideology first. What emerges is a functional pathway to violence: research, acquisition, rehearsal, reconnaissance, breach.
Political Signals Without a Through-Line
Public records capture a set of mixed political signals: a Republican voter registration; a small, one-time $15 donation as a minor that passed via ActBlue to a Democratic-aligned turnout effort; and no manifesto. Investigators and reputable outlets found no sustained engagement in militant forums or local extremist groups.
The contradiction is itself a signal. It points away from a clean ideological lineage and toward a more familiar contemporary profile: inconsistent cues, compartmentalization, and operational focus. The most defensible conclusion available to date is narrow: Crooks chose the target, prepared, and executed; he did not, in public, explain why.
The Venue and the Geometry of a Breach
The Butler Farm Show grounds are bordered by open fields and light-industrial buildings. Among them is the American Glass Research (AGR) complex, which sits outside the fenced federal footprint but within unobstructed rifle range of the rally stage. High-ground vantage points like the AGR roofs are obvious, and doctrine for outdoor events puts a premium on either securing those positions or assigning clear command ownership beyond the fence.
On July 13, that did not happen. From mid-morning onward, the flow into the rally progressed through magnetometers and screening queues. Outside the fence, unscreened spectators gathered along the AGR perimeter. Local tactical elements were tasked to watch the venue and crowd; the off-perimeter high ground was not under federal control. In the afternoon, a critical technology layer—counter-unmanned-aircraft detection and mitigation—was not effectively operating. During that outage, a small drone overflew parts of the site, aiding a would-be attacker in confirming sightlines and access routes. That lapse later became one of the most criticized gaps in the protective posture.
Day-of Movements
The documented elements of Crooks’s day align with his prior months of preparation. In the hours before the rally he purchased ammunition locally. He had acquired a five-foot ladder earlier that day, but investigative records and testimony later clarified that the purchased ladder was recovered elsewhere and not used to access the roof. A ladder visible in post-incident photographs belonged to law enforcement. He moved into position on the AGR roof by other means available on site.
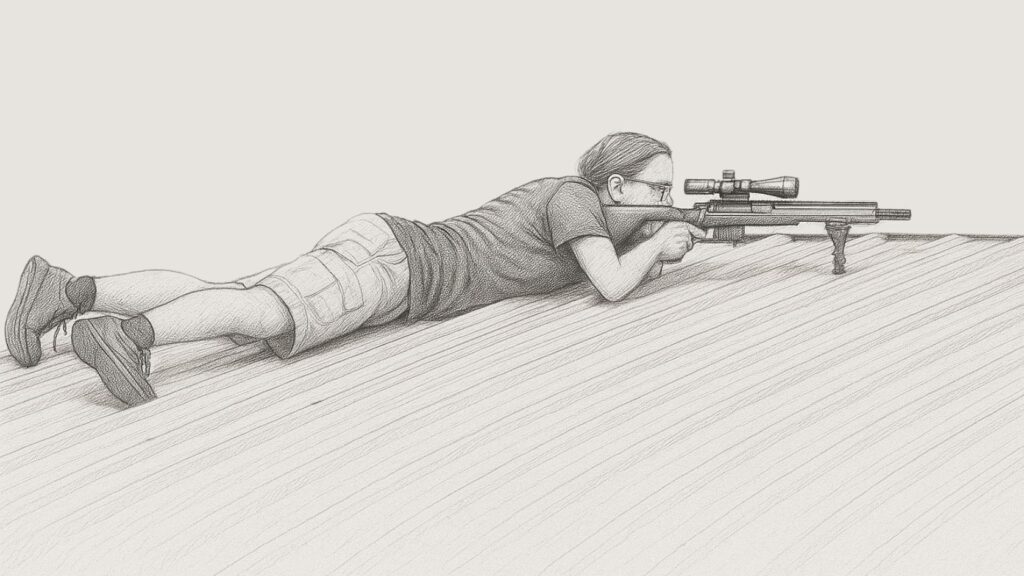
From an elevated position with a direct corridor to the lectern, he lay prone behind rooftop equipment, stabilized his view, and waited. The protectee entered the frame of fire. The clock reached 6:11 p.m.
The Attack in Seconds
Eight shots. The first clipped the protectee’s right ear. Firefighter Corey Comperatore was killed while shielding his family; two spectators suffered gunshot wounds. The protection detail executed immediate-action drills, shielding the protectee behind the lectern while marksmen established a firing solution. Within roughly a dozen seconds of the first shot, a counter-sniper killed Crooks on the rooftop. Only then was the protectee escorted from the stage. The crowd’s visible drop synchronized with the first shot, a detail that undermines later claims of foreknowledge.
The engagement window was measured in seconds, not minutes. The difference between a grazed ear and a fatal wound was a combination of lateral offset, movement, and the speed of counter-fire.
What Is Known—and What Remains Unresolved—About Motive
Absent a manifesto, the behavioral record remains the clearest lens. There is no public evidence of a directive from a group, a handler, or a co-conspirator. The search history reads like practical homework for an attack, not a catechism. Interviews with family and community produced few statements that could serve as a founding grievance. His political registration and the single small donation point in different directions.
The most disciplined conclusion available as of August 2025 is narrow: Crooks acted alone and left no coherent public rationale. The desire to impose a grand explanation where none exists has fueled much of the misinformation that followed.
The Institutional Reckoning: Doctrine Gaps and Cultural Drift
Two formal reviews—one from a bipartisan House task force and one from an independent panel commissioned through the Department of Homeland Security—characterized the Butler protective operation as preventable. The finding is stark and repeated: obvious high ground outside the fence was not under positive control; responsibility for that ground was ambiguous; a counter-UAS layer failed during a critical window; sightings of a suspicious individual on structures with line of sight were not escalated quickly through command; and on-scene leadership lacked the redundancies that doctrine presumes.
Leadership consequences followed. The Director of the U.S. Secret Service resigned under bipartisan pressure. New leadership issued policy updates on high-ground control at outdoor events, set redundancy requirements for drone detection, and revised escalation protocols for rooftop reports. Congressional oversight persisted into 2025 with a focus on resourcing and culture: whether a stressed and politicized agency can build and sustain the depth that doctrine requires.
The critiques extended beyond technical fixes. Witnesses described a drift toward procedural complacency under intense, sustained political pressure, wave after wave of threats to multiple protectees, and staffing shortages that forced improvisation. In that environment, the difference between adequate and inadequate is not always visible until it is catastrophic.
Debunking the Most Persistent Conspiracy Claims
This section isolates the most widespread claims and addresses them with the record available as of August 2025.
Claim 1: “It was staged; agents weren’t even wearing earpieces.”
High-resolution photographs and broadcast footage from the rally show agents using standard earpieces and comms. Scenes circulated online purporting to show “no earpieces” were often cropped or from different dates.
Claim 2: “The chest wound photo proves makeup, not injury.”
A widely shared still purported to show an artificial chest wound. Photogrammetric reviews and additional angles show the “wound” was a crease in fabric. Medical documentation and multiple angles of the ear laceration confirm a grazing bullet wound.
Claim 3: “Inside job—someone let the shooter onto the roof.”
The reviews document ambiguity of responsibility for the AGR complex, technology downtime, and missed escalations. Those are failures, not permissions. There is no credible evidence of foreknowledge by federal or local officials.
Claim 4: “The ladder proves coordinated access.”
Receipts and testimony confirm Crooks bought a five-foot ladder. Investigators later recovered that purchased ladder elsewhere. The ladder visible in post-incident footage was law enforcement’s. Roof access was gained by other means present on site.
Claim 5: “There had to be a second shooter or remote explosive trigger.”
Explosive components and two viable IEDs were found unused. The ballistic and timeline record of the eight shots and the counter-sniper engagement show no second shooter. The devices increase the seriousness of preparation; they do not imply external coordination.
Claim 6: “He was clearly left-wing/right-wing; the record proves it.”
The record proves inconsistency: a Republican registration, a single small donation routed via ActBlue to a Democratic-aligned turnout group when he was a minor, and no manifesto. Attempts to settle the question with a partisan label go beyond what the public evidence supports.
Claim 7: “Trump knew; the crowd’s reaction proves staging.”
Audience reaction videos show the crowd behind the lectern dropping in synchronization with the first shot and agents shielding the protectee until the shooter was neutralized. The sequence is consistent with surprise and immediate-action drills, not foreknowledge.
Conspiracies thrive on anomaly hunting and evidence deserts. Butler offered both: grainy images, a fast event, a protectee with a complex political orbit, and a shooter who left no narrative to argue with. The absence of motive is not proof of anyone else’s.
Political and Cultural Aftermath
The attempted assassination became a mobilizing symbol for the Trump campaign. A single frame—blood on the ear and a fist raised—operated simultaneously as proof of peril, perseverance, and providence. The image did what powerful images do: it compressed complexity into a transmissible emblem supporters could rally around. Fundraising emails and rally speeches integrated the motif within hours.
For the administration then in office, the incident forced a public accounting on protection doctrine and agency leadership. The response required condemning political violence while acknowledging that failures occurred on their watch. Congressional hearings had both substantive and theatrical elements: substantively, lawmakers pressed the agency on high-ground control, counter-UAS redundancy, and escalation discipline; theatrically, members sought clips that dramatized accountability or shifted blame.
Outside Washington, western Pennsylvania communities absorbed the collision of the familiar with the catastrophic. Bethel Park and Butler—places defined in the national imagination by tidy lawns, youth sports, volunteer fire halls, and county fairs—became a stage for a very modern American story: the lone actor with method and opportunity, the small failures that scale catastrophically, and the spectacle that makes politics out of pain.
The Information Environment: Ambiguity as Opportunity
In the hours and days after the shooting, social platforms became the venue where fear and grainy images metastasized into narrative. The event offered everything that fuels engagement engines: a famous target, live-streamed chaos, still photos that can be cropped into apparent anomalies, and a vacuum where motive would ordinarily sit. In such environments, “anomaly equals conspiracy” is a default setting, not a conclusion.
The demand for meaning collided with the supply of partial facts, and the result was a market: influencers selling explanations, opportunists converting grief into metrics, and partisans weaponizing uncertainty. Those dynamics complicate both public understanding and policy response. When ambiguity hardens into conspiracy, institutional legitimacy erodes, and reforms—however necessary—are dismissed as cover stories.
Lessons for Protective Doctrine and Public Life
First, outdoor protective operations must assume that perimeter fences do not define operational reality. High ground with line of sight to a stage must be under positive control even when it sits beyond the “hard” federal footprint. That control has to be owned explicitly in the plan and verified on the day.
Second, consumer drones are a persistent risk. Counter-UAS capability must be redundant, continuously monitored, and integrated into the command rhythm. It is not a “nice to have”; it is a core layer of the modern stack.
Third, escalation discipline is a human skill, not merely a policy. When multiple civilians or officers report suspicious rooftop behavior, the system must convert those inputs into immediate action. The Butler record shows how delay compounds.
Fourth, prevention in lone-actor cases is less about ideology screening than about closing seams in physical and technical protection and training personnel to act decisively on behavioral triggers. The toolchain—what was bought, built, practiced, and rehearsed—is often the only “ideology” a lone actor leaves.
Fifth, the information aftermath needs a posture, too: transparent timelines, prompt release of core facts, and explicit labeling of uncertainty reduce the oxygen available to speculation. Silence invites invention.
A Portrait Without Myth
There is no need to mythologize Crooks to explain what he did. He was an academically successful community-college graduate with a transfer plan; a part-time employee with a clean record; a son who kept his inner life largely to himself; a methodical shooter who practiced frequently; a tinkerer who assembled devices he never used; a planner who exploited a small set of avoidable vulnerabilities. He was twenty years old. His act ended his life, took another, injured others, and exposed gaps in institutional readiness that have been discussed for years and too often deferred.
This is precisely what makes lone-actor violence so difficult to predict and discourage. It does not always announce itself with a movement, a forum, or an essay. Sometimes it arrives as a competence quietly cultivated, a toolkit assembled, and a target chosen.
Why Butler Matters in 2025
The most durable risks illuminated by Butler are practical. Campaigns increasingly rely on open-air spectacle; consumer drones are cheap and ubiquitous; small agencies with limited staffing are folded into complex command diagrams at short notice; political meaning is minted and weaponized in minutes. The doctrine that protects public figures has to be resourced to meet those facts, not the facts of a prior decade. And the information environment that metabolizes such events has to be understood as an operational consideration, not a public-relations afterthought.
Policy responses that overcorrect—turning campaigns into sterile, inaccessible fortresses—risk eroding the democratic openness they intend to safeguard. The better path is ordinary rigor: control the high ground; keep the sensors up; staff the plan with depth; rehearse and reward aggressive escalation when suspicious rooftop movement is reported; publish verified facts fast.
The Families
Public discussions often flatten victims into footnotes. They should not be. Corey Comperatore’s family absorbed an irreversible loss in a scene of chaos they did not choose. Two other families live with injuries that compel an ongoing, private kind of courage. Crooks’s parents, who did not choose any of this either, now live with the wreckage of a son’s decision and a nation’s reaction. In a healthier information culture, these families would not have to wade through what followed—performative suspicion, online harassment, and the endless recycling of claims that the evidence has already answered.
What Changed—and What Must Still Change
Some reforms were implemented: leadership turnover, doctrine updates on high ground, counter-UAS redundancy requirements, and clarified command ownership for off-perimeter structures with line of sight. Those changes matter. But reforms on paper do not protect stages; people do. The question that remains live in 2025 is whether training, staffing depth, and organizational culture will sustain the discipline doctrine prescribes when the next open-air event presents the same geometry: high ground just beyond the fence, a technology layer that can fail, and a small but decisive window where rooftop reports must be acted on now.
The parallel question for public life is whether we can defend meaning with the same discipline: labeling uncertainty, rejecting the translation of anomaly into conspiracy, and refusing to turn genuine failures into omnipotent plots. Butler is a case study in avoidable vulnerability; it is not a template for a hidden state.
Conclusion
Thomas Matthew Crooks did not act on behalf of a cell or a handler. He did not leave a treatise for commentators to mine. He did what many lone actors do in the modern era: he learned what he needed to learn, practiced until competent, acquired what he needed to acquire, and exploited an avoidable seam in protection to attack a famous target. The breach was brief; the resonance has been long.
The reforms now underway can harden venues against the next actor’s method. Whether the political and information cultures can harden themselves against the next wave of opportunism—turning seconds of fear into years of story—is a separate test. Butler will remain a marker not because of who Crooks was, but because of what the attack revealed: a protection doctrine that must be resourced to reality, and a public square where ambiguity is either managed responsibly or milked until nothing solid remains.
Sources (selected; accessed August 17 to 19, 2025)
- U.S. House of Representatives. Findings of the Task Force on the Attempted Assassination of Donald J. Trump on July 13, 2024. House Report (December 2024).
- Department of Homeland Security. Independent Review Panel: Assessment of the July 13, 2024 Protective Operation. (2024).
- CBS News Investigations. “The Secret Double Life of Thomas Crooks” (July 11, 2025); “Crooks’ Emails and Essays” (May 23, 2025).
- Reuters. “What We Know About Thomas Matthew Crooks” package; and fact-checks on viral claims related to the Butler rally (July–August 2024).
- The New York Times. “Thomas Crooks: The Shooter’s Path in the Year Before Butler” (June 8, 2025).
- PBS NewsHour. Live and follow-up reporting on the Butler rally shooting (July 2024).
- Snopes. “Did the Trump Rally Shooter Donate to a Democratic Group?” (July 2024).
- Congress.gov. House oversight hearing materials and FBI testimony summaries (2024–2025).
- Associated Press; Washington Post; ABC News; WESA; Pittsburgh Post-Gazette. Background on schooling, employment, range membership, and day-of timeline (July 2024–May 2025).
- U.S. Secret Service / DHS public statements. Counter-UAS posture and outdoor venue doctrine updates (2024–2025).